This report covers 410f9ad to 2f953d304e
The biweekly cadence messed up my timing so this report covers five weeks and for that reason gets to report more development (314 commits).
The biggest chunk (over one third of the commits) covers Intel Skylake development, where boards and chipset code saw misc improvements and tons of clean ups (eg. dropping ACPI code and fragments in the devicetrees that were inherited from older chipset development and aren’t appropriate anymore).
There also was a notable effort of unifying common code across the more recent Intel SoCs, removing lots of duplicated code all over the place.
As far as cleaning up the code base goes, we also got rid of a number of Kconfig definitions and uses across the tree (Intel, AMD, MIPS – something for everybody). Some definitions were booleans that were always enabled with no reason to ever disable, other symbols were selected even though they didn’t even exist anymore.
Another field of clean-up work was the EDID code used for native graphics init, which is the default on ARM SoCs (simply because there is nothing like VGABIOS there). Two structs that both defined standard fields of this “Extended Display Identification Data” standard were reworked to avoid the duplication, avoiding issues where a field is filled in for one representation but not the other.
On x86, the romstage is now relocated for its final location in CBFS by cbfstool, obsoleting the old approach that had us link it twice, once to determine its final size and then to the actual location it’s supposed to run from. This reused code from our rmodule support that already contained knowledge about relocation fields.
In the future this same approach may be extended to other files that need to be executed in place such as the FSP binary.
This effort also had x86’s linking setup become more similar to what all other architectures are doing, for romstage and ramstage, as well as some more clean-ups in the general area.
Finally, the way the romstage is linked together was simplified, resulting in less “magic” in the build system to collect the various pieces of initialization code.
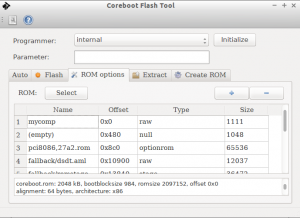
The romstage change eliminated the need for cbfstool’s “locate” command, and so it was removed. cbfstool also saw other extensions, the biggest one a compatible change to the format to allow for per-file attributes in CBFS. These attributes can contain additional information about a file, currently the compression method and uncompressed size of a file. cbfstool and the build system were extended to allow compressing files, libpayload is able to uncompress these files.
The libpayload change leads to a change in behavior for some specialized cbfs access routines (eg. cbfs_load_optionrom) in that they return malloc’d memory instead of a pointer into CBFS, which may lead to a memory leak in payloads.
cbfstool’s support for flashmap “partition tables” was also improved: It already could create flashmap partitioned images, and now can create a backward compatible CBFS master header, so an fmap-based image can still be used by older CBFS parsers (which right now means: pretty much all of them).
If an fmap is available, cbfstool will prefer it over a master header, but that should have no visible effect yet.
The changes also seeked to improve the internal structure of the cbfstool codebase, although much more work is necessary in that area.
libpayload saw the addition of a video_printf function to write colored text with support for text justification.
Its USB device controller driver for DeviceWare based controllers became more robust, too.
It also got back a POSIX-compatible ffs() implementation that was dropped for a while, got coreboot-compatible write8/16/32 implementations and saw a couple of bugfixes.
Another clean-up topic is the reduction of code that is #ifdef’d away for invidivual stages. To this end, we now expose declarations (but no definitions) for various functions even in romstage, so files compile. Use of ramstage-level functions like malloc in romstage still fail, but at link time. The linker is smart enough these days to pinpoint the error to a line in a source file, so no information is lost. The upside is that the code flow isn’t broken by preprocessor conditionals every few lines.
In a similar light, more #if CONFIG_FOO statements were replaced by if (IS_ENABLED(CONFIG_FOO)), exposing the guarded code to the compiler, which avoids errors from accumulating in non-standard configurations: Now the code needs to pass the compiler at least syntactically even in a standard configuration.
Finally, Chrome OS vboot related code was abstracted away in SoC code, to make it more useful in non-Chrome OS configurations more easily.
To reduce code duplication, we also started building a common library (src/commonlib/), containing things like CBFS data structure declarations or endianess handling functions that are useful in both coreboot and its utilities.
On the AMD side, there were various bugfixes both for new (merlin falcon) and old (Fam10) chipsets.
ARM64 and Tegra210 saw various bugfixes and improvements to power use. For the latter, coreboot also learned how to reserve memory for other functions than the main processor.
Rockchip’s RK3288 ARMv7 SoC also saw a number of bug fixes and the code was restructured to use a single mainboard directory for a large number of very similar Google Veyron mainboards based on that SoC.
Our RISCV support now boots on the Spike simulator which (besides supporting a wider variety of emulators) is notable because unlike the QEmu RISCV support, Spike supports RISCV’s revised ABI.
Speaking of emulators, recent versions of qemu-x86 expect the firmware to initialize the LAPIC, which we now do.
The timestamps recording code was extended to also store the timebase (ticks) so that the userspace tool in the OS doesn’t need to try to figure it out – probably wrongly because by the time the OS started, the clock changed and with it, on some CPUs, the tick duration.
cbmem also gained an option “-T” to display timestamps in a machine readable format.
During the course of that development, some timestamps code was simplified, relying more on generic code over per-chipset implementations.
The ongoing effort to move CPU microcode into CBFS (and to store these as binaries in 3rdparty/blobs instead of header files in the main sources) saw some progress.
Our crosscompiler generator script is more helpful on errors and learned building gcc (the “GNU compiler suite”) for non-C languages, including some extensions to support Ada in particular.
abuild now produces proper logs when building the tools (below util/), making it easier to track down issues in that area from error reports on our continuous build system.
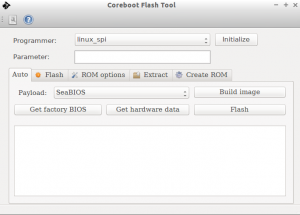
The standard seabios released used by our build system is now 1.8.2, up from 1.7.5. In other payload related news, coreboot doesn’t initialize PS/2 keyboards by itself by default, but expects the payload to do so. The option to re-enable the initialization (as well as the code it controls) is still around.
The intel-related utilities saw some improvements, with ifdtool supporting the new IFD v2 better (as used on Skylake), and inteltool able to detect Intel’s 4-Series.
The tree also saw some improvements with regard to portability and should behave better when building on MinGW, Cygwin, Mac OS X and FreeBSD host.